-
Welcome to Overclockers Forums! Join us to reply in threads, receive reduced ads, and to customize your site experience!
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Western Digital Gold appears to go to sleep minutes after last use
- Thread starter c627627
- Start date
- Joined
- Feb 18, 2002
- Thread Starter
- #102
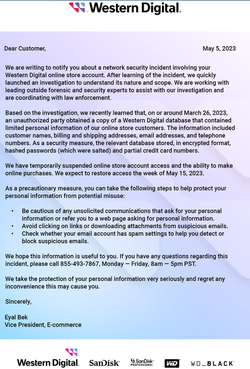
They're one of the biggest data storage manufacturers in the world.
If your data is not safe with a company like that in 2023, it would be interesting to know if this is due to negligence [lapse due to unpatched, unsecure, unmonitored network] or if today, any data with any company could be accessed by third parties who are powerful enough? I mean we've seen this before but technically, we never talk about the details of how and why it happens.
If your data is not safe with a company like that in 2023, it would be interesting to know if this is due to negligence [lapse due to unpatched, unsecure, unmonitored network] or if today, any data with any company could be accessed by third parties who are powerful enough? I mean we've seen this before but technically, we never talk about the details of how and why it happens.
- Joined
- Oct 16, 2014
- Location
- Allagash, Maine
Whats our policy on conspiracy theories and poor people again? lolol
- Joined
- Feb 18, 2002
- Thread Starter
- #104
What I'm asking is, there are two options, someone in IT at Western Digital not doing their job or some sort of an unknown exploit no one could defend against?
In the past there were news stories about laughable security measures at some of these companies... Or is this about they were fully patched and secured, but it could have happened to any company because there was no defending against what ever the exploit was?
In the past there were news stories about laughable security measures at some of these companies... Or is this about they were fully patched and secured, but it could have happened to any company because there was no defending against what ever the exploit was?
- Joined
- May 29, 2005
Almost always the exploit for a lot of these compromises comes through social engineering or similar. Or an unsecure cloud storage container etc (which would go into someone at some level of rights making a dumb choice (or using live snapshot data in a test dev environment which may not be as secure))
- Joined
- Jun 21, 2002
Yeah I usually assume it's someone gets phished. Honestly its statistical at this point, even the smartest most security conscious individual can be phished if the attack looks good enough and is opened at just the right point when the person is stressed out, distracted or rushed enough.
- Joined
- Feb 18, 2002
- Thread Starter
- #107
Stay on that for a moment - does it require entering, typing info (giving info away to hackers)?
Or is it enough to give away the farm by simply opening a malicious email, just to see what it is?
If it's the former, I mean, you can quickly and easily see by the web address in the address bar, or by simply hovering over the link, that it points to a "phishy" location.
Or is it enough to give away the farm by simply opening a malicious email, just to see what it is?
If it's the former, I mean, you can quickly and easily see by the web address in the address bar, or by simply hovering over the link, that it points to a "phishy" location.
- Joined
- May 29, 2005
A bit of both. Many people will use url shortener or mask the url with a very similar looking one. Some companies(like the one I work at) have a url filtering service in our cloud outlook, which is largely useful, but it mostly obfuscates the url into hundreds of characters.
Then there's very targeted spear phishing attacks as well. And websites that are made to look virtually identical to the known site to capture credentials.
There's also numerous, large data breaches, some of which captures user and password data. If that isn't encrypted, then that's another source of guessable passwords.
You have man in the middle and supply chain attacks, where a hacker adds a vulnerability to a popular product or service (solarwinds was somewhat recent) which is used by companies large and small.
Then there's places that don't require mfa as well.
And all of those are tech based and not including rogue employees, blackmail, etc
Source: been in IT for 15 years and sat through plenty of cyber security presentation, change management calls, and listen to net sec podcasts that talk about it every few days.
Then there's very targeted spear phishing attacks as well. And websites that are made to look virtually identical to the known site to capture credentials.
There's also numerous, large data breaches, some of which captures user and password data. If that isn't encrypted, then that's another source of guessable passwords.
You have man in the middle and supply chain attacks, where a hacker adds a vulnerability to a popular product or service (solarwinds was somewhat recent) which is used by companies large and small.
Then there's places that don't require mfa as well.
And all of those are tech based and not including rogue employees, blackmail, etc
Source: been in IT for 15 years and sat through plenty of cyber security presentation, change management calls, and listen to net sec podcasts that talk about it every few days.
Last edited:
- Joined
- Jun 21, 2002
My point is people are fallible. All people, regardless of age, experience, intelligence or education make mistakes. You can successfully avoid 10,000 attacks, but it only takes missing it one time. Multiply this by all the people in the company and it begins to seem more like an inevitability than a mistake. This paradigm is what keeps air travel safe and is slowly working to improve the safety of medicine (though much of the field is still run by egos sadly).
- Joined
- Feb 18, 2002
- Thread Starter
- #110
No more hard drives will be sold after 2028

 blocksandfiles.com
blocksandfiles.com
They're saying "The disk/flash crossover event is closer than you think..."
What do you guys think, how long before 16TB SSD is under $300?

Pure: No more hard drives will be sold after 2028 – Blocks and Files
A Pure Storage exec believes no more hard disk drives will be sold after 2028 because of electricity costs and availability.
They're saying "The disk/flash crossover event is closer than you think..."
What do you guys think, how long before 16TB SSD is under $300?
Hello all and to the OP of this very interesting thread.
I've just registered for the first time to offer some info/experience re your recalcitrant WD Gold HDD. Did you ever get this solidly resolved?
I have a number of Gold and Ultrastar drives (basically they are exactly the same drives) in various sizes. I have a 12 TB Gold, 2x 14TB Ultrastars, 2x 14TB Gold and 1x 18TB Gold. had them all over 4 years except for the 18TB which is 2 years.
All of my above drives were bought brand new from a reliable and reputable bricks & mortar shopfront in my local area. I also have a little WD 1TB 10,000rpm Raptor HDD from 2012 that's never missed a beat and still revving it's little heart out! Tech marches on though and all my 7,200rpm drives are quicker than it now.
Ok, so, on to my experience with my Gold and Ultrastar drives. All my drives are attached to the PC I use for 4K & 8K video editing. Here's the kicker: Don't fall off your chair but I still run Win7 Pro in SEPT 2023! Long story short I have some older programs I still need to use that Win7 does very well. Win7 also runs all the vid editing progs I use so I stuck with it - wasn't broken. Suits my moderately 'older' PC anyway.
My story with my HDDs is quite boring. I'm here to tell you I do NOT believe they are manufactured to spin down at any time unless you have Windows set to do it. You don't have Win set to do it. Simple. I have never had or heard any of my drives spin down. I have some plugged as normal into the MoBo and some are in an Icybox external USB 3.1 box. I have never had any delay whatsoever accessing the Gold, Raptor or Ultrastars.
There is ZERO mention of any spin-down capability mentioned in any of the Gold or Ultrastar marketing material (I wouldn't have bought otherwise). Further, these drives are ALSO recommended for desktop (not just corporate) by many reputable reviewers. They are CMR drives so ultimately compatible with all desktop Windows systems - same as any garden variety SATA HDD.
I do believe strongly that spinning any drive down and up again multiple times a day WILL affect their longevity and that's why my Win7 pro is set to NEVER spin down - just like your setup. Are you on Win10? I imagine you are, or Win11?
There's only one thing I'd check if I was you. Maybe your BIOS has settings for INDIVIDUAL drive spin-down? Maybe your black drive is set in the BIOS separately to your gold drive? I don't know for sure but there are some odd BIOSs out there over the years. If that isn't the issue then I'd most definitely be taking WD up on their offer to replace the drive. While Gold and Ultrastar are generally THE most reliable on the market BAR NONE, everyone knows that the odd manufacturing fault can afflict the best of big names. Nothing/no one is perfect. Good luck with your Goldie!
I've just registered for the first time to offer some info/experience re your recalcitrant WD Gold HDD. Did you ever get this solidly resolved?
I have a number of Gold and Ultrastar drives (basically they are exactly the same drives) in various sizes. I have a 12 TB Gold, 2x 14TB Ultrastars, 2x 14TB Gold and 1x 18TB Gold. had them all over 4 years except for the 18TB which is 2 years.
All of my above drives were bought brand new from a reliable and reputable bricks & mortar shopfront in my local area. I also have a little WD 1TB 10,000rpm Raptor HDD from 2012 that's never missed a beat and still revving it's little heart out! Tech marches on though and all my 7,200rpm drives are quicker than it now.
Ok, so, on to my experience with my Gold and Ultrastar drives. All my drives are attached to the PC I use for 4K & 8K video editing. Here's the kicker: Don't fall off your chair but I still run Win7 Pro in SEPT 2023! Long story short I have some older programs I still need to use that Win7 does very well. Win7 also runs all the vid editing progs I use so I stuck with it - wasn't broken. Suits my moderately 'older' PC anyway.
My story with my HDDs is quite boring. I'm here to tell you I do NOT believe they are manufactured to spin down at any time unless you have Windows set to do it. You don't have Win set to do it. Simple. I have never had or heard any of my drives spin down. I have some plugged as normal into the MoBo and some are in an Icybox external USB 3.1 box. I have never had any delay whatsoever accessing the Gold, Raptor or Ultrastars.
There is ZERO mention of any spin-down capability mentioned in any of the Gold or Ultrastar marketing material (I wouldn't have bought otherwise). Further, these drives are ALSO recommended for desktop (not just corporate) by many reputable reviewers. They are CMR drives so ultimately compatible with all desktop Windows systems - same as any garden variety SATA HDD.
I do believe strongly that spinning any drive down and up again multiple times a day WILL affect their longevity and that's why my Win7 pro is set to NEVER spin down - just like your setup. Are you on Win10? I imagine you are, or Win11?
There's only one thing I'd check if I was you. Maybe your BIOS has settings for INDIVIDUAL drive spin-down? Maybe your black drive is set in the BIOS separately to your gold drive? I don't know for sure but there are some odd BIOSs out there over the years. If that isn't the issue then I'd most definitely be taking WD up on their offer to replace the drive. While Gold and Ultrastar are generally THE most reliable on the market BAR NONE, everyone knows that the odd manufacturing fault can afflict the best of big names. Nothing/no one is perfect. Good luck with your Goldie!
Similar threads
- Replies
- 2
- Views
- 9K
- Replies
- 16
- Views
- 17K
- Replies
- 3
- Views
- 4K
- Replies
- 5
- Views
- 2K